Hackers are always coming up with new ways to send malware. Typically, malware is sent to a user via phishing emails when the user accidentally downloads the malware by clicking on a link or attachment within the email. However, hackers are starting to become more versatile in their attack distributions and are beginning to utilize Google Drive to deliver malware to users.
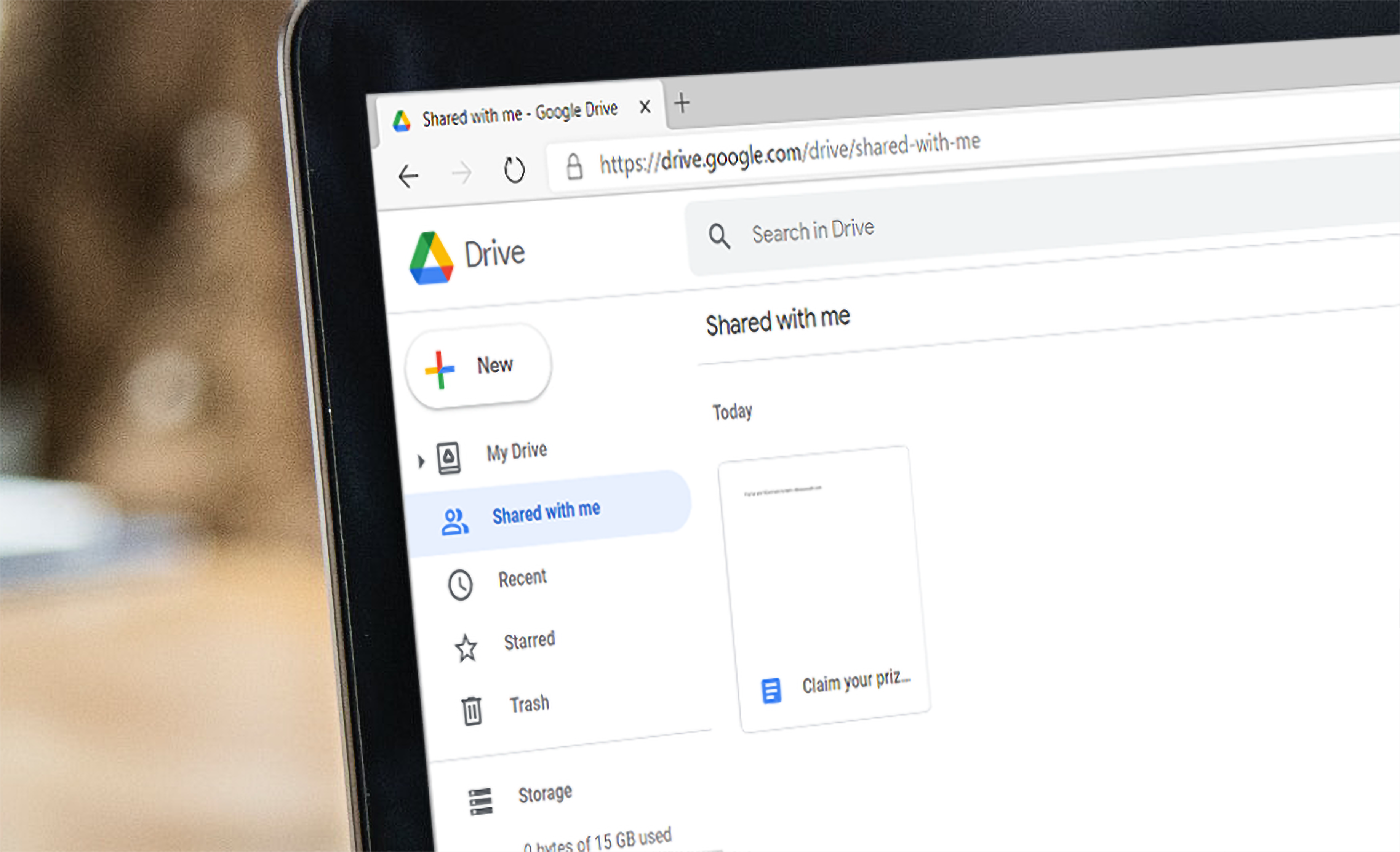
A variety of organizations around the world use Google Drive. It serves as a cloud storage platform for various file types, including documents, spreadsheets, photos, videos, and presentations. Many companies utilize Google Drive because it provides a way for multiple employees to collaborate on a single file at the same time. Moreover, employees can create files and share them with other employees via an email invite. The problem with this is that hackers are starting to utilize the email invitation feature as a means to lure users into clicking on malicious links. Hackers do this by first creating a document containing an enticing “prize winner” message. The message will state that the user has won a prize and that they must click a link to get redirected to a website where they will receive it. However, the link is actually malicious and will download malware onto a user’s computer as soon as they click the link. Hackers have had a lot of success from utilizing Google Drive. Most of this success comes from the fact that the email containing the malicious link sends from a Google email address. That is due to the automated invitation email sent from Google whenever someone shares a document with another user. Hackers utilize this feature to make the email appear legitimate and thus bypass email firewalls and other security controls.
Now more than ever, it is crucial to pay close attention to content within emails. Even emails sent from a verified source can contain malicious links or attachments. Fortunately, Google is aware of this dangerous tactic and is currently working on a plan that will help to detect Google Drive spam. In the meantime, here are a few things to keep in mind that will help protect you from this Google Drive attack.
Are you expecting a shared file from Google Drive?
Typically, users are aware when they are going to receive a shared file via Google Drive. However, when an unexpected email pops up and states that someone has shared a file through Google Drive, it could be malicious. If you receive an invitation to access a file via Google Drive that you were not expecting, contact the sender directly and verify that the email is legitimate.
What type of file was shared?
These Google Drive attacks accomplished by using Google documents. These documents usually contain information about a prize and will suggest that the user clicks a link. While it may seem like common sense not to click on the “prize” link, many users fail to do so. Remember to assess each shared document and never click any links unless you are sure that they are not malicious.
Does the document contain poor grammar?
You would be surprised by the number of hackers that do not proofread before conducting an attack. Misspelled words and other types of grammatical errors can be signs of phishing. Make sure to read the entire document and assess the grammar and language used. Also, look for signs of urgency. Hackers will use language that creates a sense of urgency to get the user to act quickly. Generally, these two signs are indicative of a phishing attempt.
Hackers continue to develop better ways to deliver malware to their victims. Hackers have used Google Drive countless times to send malware to users, and they will continue as long as it works. Therefore, we must assess each email and document carefully. Never open any attachments or links unless you are sure that they are legitimate, and when in doubt, contact the sender directly to verify that they were trying to share something.